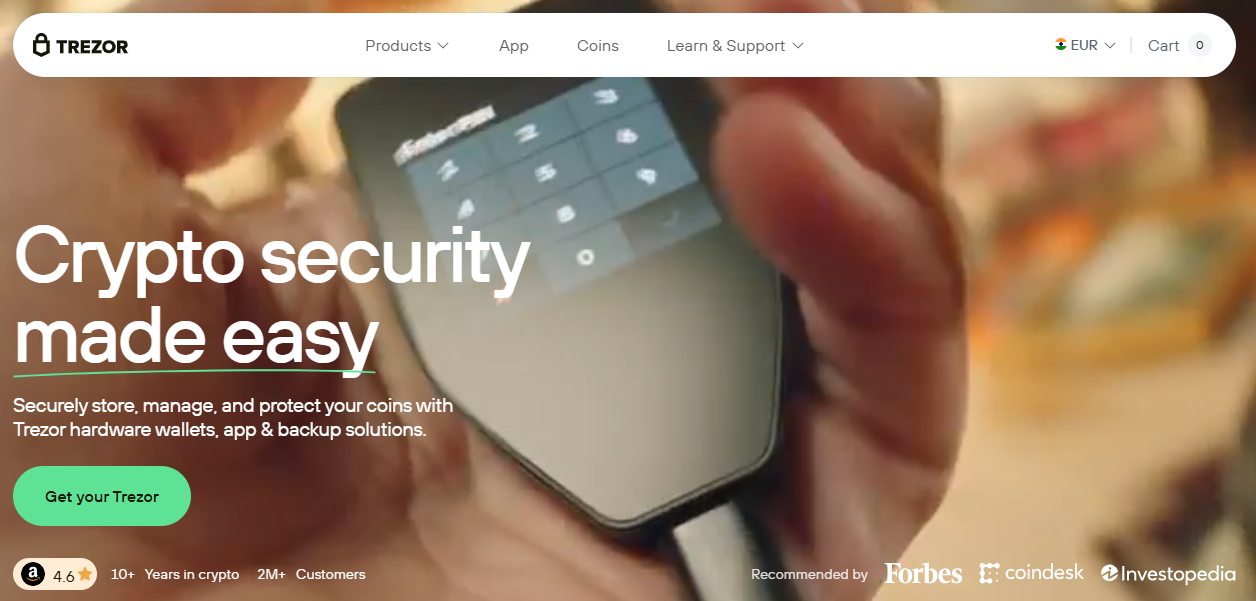
Trezor Login is the official gateway for users who wish to securely access and manage their cryptocurrency portfolios through the Trezor official website. As one of the world’s most trusted hardware wallet solutions, Trezor ensures that your private keys never leave your device — giving you complete control and security over your digital assets.
The Trezor Login process allows users to connect their hardware wallets to Trezor Suite — the official desktop and web application for managing cryptocurrencies. This secure login bridge ensures that all authentication happens offline within the Trezor device, keeping sensitive data like PINs and recovery seeds isolated from online threats.
By logging in through Trezor Login, you gain direct access to portfolio management tools, coin sending and receiving features, and advanced settings like passphrase protection or hidden wallets — all handled through Trezor Suite’s trusted interface.
Follow these steps to access your Trezor Login safely and efficiently:
Once logged in, you will see your portfolio dashboard, account balances, and available cryptocurrencies. All communication between your device and the suite is end-to-end encrypted for maximum protection.
Trezor Login uses industry-leading security protocols to ensure complete data safety. The core security principle behind Trezor is isolation — your private keys never touch the internet. Authentication, transaction signing, and seed management are all handled within the device.
Here are the key layers of protection:
The Trezor Login process isn’t just about accessing your crypto wallet — it’s about maintaining total sovereignty over your funds. Here’s what makes it stand out:
Every time you initiate a Trezor Login, you are engaging with one of the most trusted crypto security environments available today.
Although Trezor Login is designed to be seamless, users might occasionally encounter login difficulties. Common solutions include:
If problems persist, visit the Trezor Support Center for official guidance.
To make the most of your Trezor Login sessions, follow these essential security practices:
Practicing these guidelines ensures your Trezor Login remains secure and resilient against online threats.
One of the most efficient ways to use Trezor Login is through the Trezor Suite application. It provides both a desktop and browser version for easy account access, complete with portfolio tracking and transaction history. The software automatically detects your connected Trezor hardware wallet and verifies its authenticity before login approval.
All actions performed within Trezor Suite — whether sending funds or adding new accounts — must be confirmed on the device itself. This hands-on verification prevents remote tampering and reinforces the security-first philosophy that defines Trezor.
In the rapidly evolving world of digital finance, Trezor Login provides an unmatched combination of convenience and security. Through verified tools like Trezor Suite and Trezor.io/Start, users can interact with their cryptocurrencies confidently, knowing that their private keys and transaction data are always safe. Whether you are a beginner or an experienced investor, Trezor remains the gold standard for secure crypto management.
Disclaimer: This content is for educational purposes only. Always access Trezor Login through the official Trezor website. Never disclose your recovery seed or private credentials to anyone. Cryptocurrency involves risk — proceed responsibly.